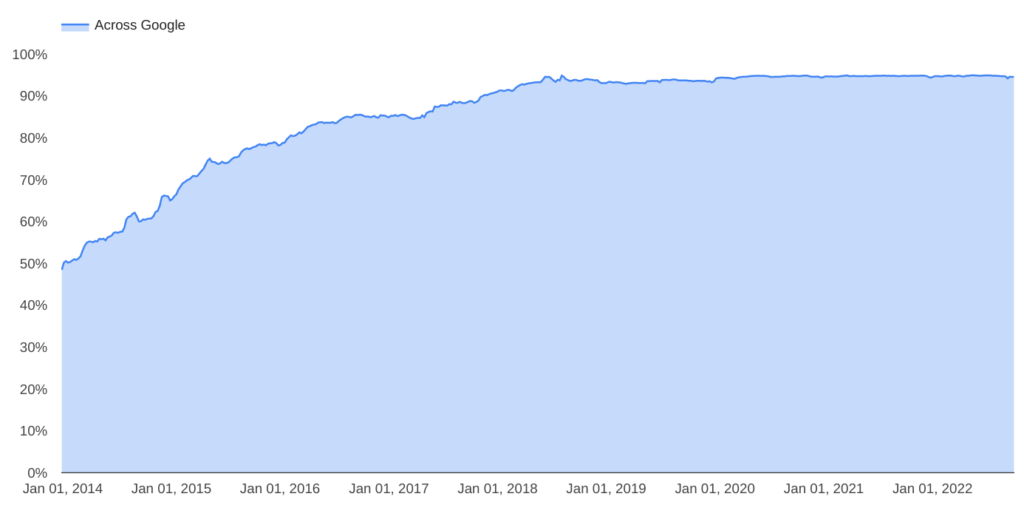
Eight years ago, 50% of the traffic to Google was in HTTP. Today Google boasts of over 95% of the traffic being secured by HTTPS. This unprecedented transition required a lot of industry-wide partnerships across multiple organizations.
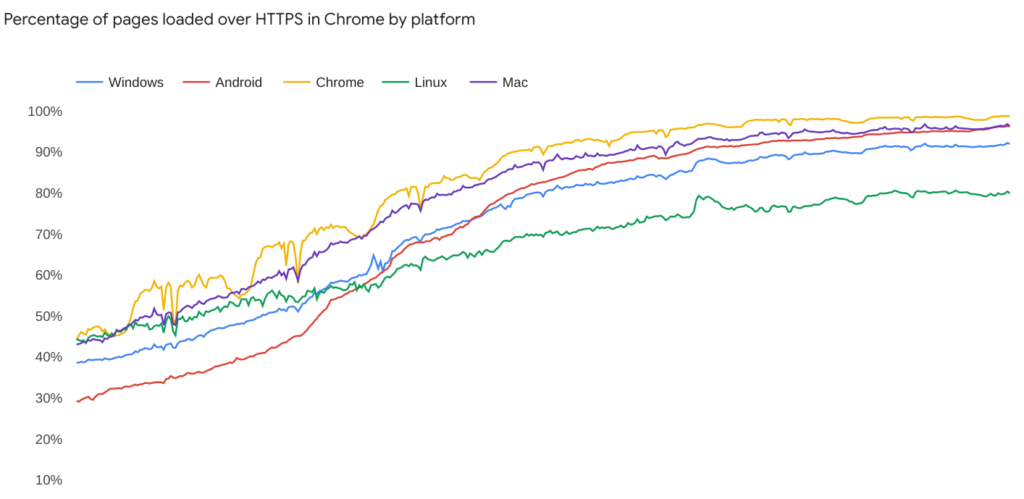
The biggest change I noticed was on Chrome on Android which moved from 29% to 96% HTTPS in the same period. I suspect the changes here were made through Chrome and Android changes over the years, and while Google hasn’t been able to move the ecosystem to 100% HTTPS, thats pretty darn close.
Read more about the current stats here.
This particular site uses lets encrypt which provides free SSL cert updates in a silent/automated way. Gone are the days when one had to pay $50 for a cert. There is absolute no good reason for anyone to keep HTTP running.
Leave a Reply