Debugging why a device is not enforcing certain policies can sometimes be painful. This tutorial should help you speed this up.
ChromeOS, unlike most other operating systems, doesn’t give you too many ways to look at system settings using a shell/script. But what you can do is look at its policies using the browser.
You can do this by going to chrome://policy page which may look something like this:
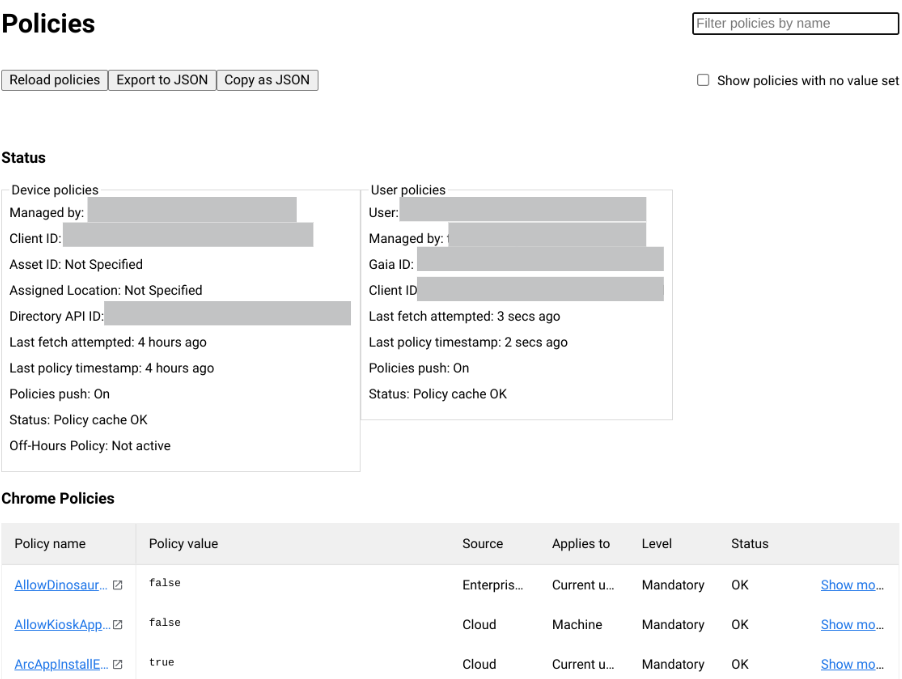
There are three parts of this you should pay attention to
Device policies
- If this section exists, you will know that your device is fully enrolled.
- “Managed by” will tell you who has enrolled you. For example if your device is part of xyz.com, it will say “xyz.com” next to “Managed by”.
- “Last fetch attempted” and “Last policy timestamp” will tell you if the device is having any issues pulling policies. If it has pulled the policy in the last 24 hours, its a good sign that everything is good.
- “Policy push: On” means that if there are policy changes made by the admin, the device will get policies pushed down from the management server immediately. Based on my experience as long as there are no connectivity issues, the policies are pushed within a few minutes.
User policies
- The existence of this block will tell you if the user who signed into the device has any policies being pushed from the server.
- “Managed by” will again tell you which domain is managing the policies. Typically, if the user’s email address is abc@xyz.com, then the “Managed by” should be “xyz.com”. However there are some edge cases where that may not be true.
- “Last fetch attempted” and “Last policy timestamp” should again tell you if the device has the latest user policies.
Chrome policies
This section will show you all the user and device policies.
- The “Applies to” field will either say “Current user” or “Machine”. “Machine” means the policy was pushed as a device policy, otherwise it was pushed as a user policy.
- Clicking on the policy name will take you a detailed page about the policy.
- For example clicking on “AllowDinosaurEasterEgg” will take you here. This gives admins and users ability to understand what each of the policies do.
- For this test, I set this policy to “false” which basically disables the Dino game [ chrome://dino ]
- When I try to start the dino game it tells me “the owner of this device turned off the dinosour game”
- If you click on “more” it will expand the “value” column. This is more useful if the value is much longer (like a json string)
Some fun facts
- These are not just useful on ChromeOS, you can use this on Chrome in Windows, Mac or linux as well. The only difference is that you would only see the “user policies” on those devices.
- You can click on “Reload policies” to re-fetch the user policies. This can be used to test network firewalls.
- Export and Copy as JSON, could be useful to extract this data as JSON file to send to someone who is troubleshooting the policies.
Leave a Reply Cancel reply